Expanding Threats Target Critical Trust Systems
1) Executive Summary
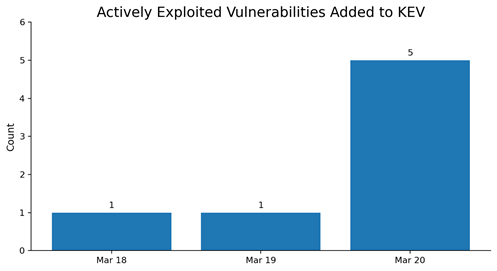
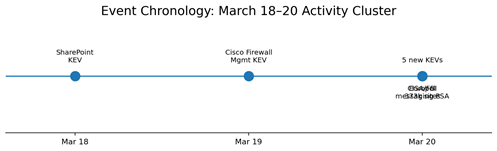
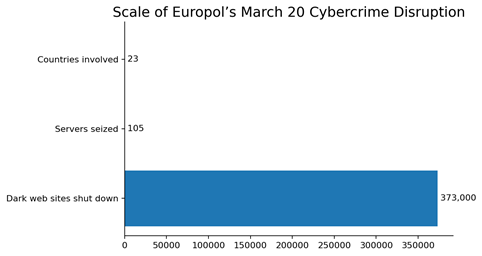
This week’s signal was dominated by rapid KEV expansion and growing risk in the systems that manage trust: SharePoint for internal collaboration, firewall management layers for network control, messaging platforms for executive communications, and common web frameworks for application delivery. The most operationally relevant items were CISA’s March 18 addition of an actively exploited Microsoft SharePoint flaw, CISA’s March 19 addition of an actively exploited Cisco firewall management flaw, five more actively exploited vulnerabilities added on March 20 affecting Apple products, Craft CMS, and Laravel Livewire, and a joint CISA/FBI warning that Russian intelligence-linked actors are targeting commercial messaging application accounts through phishing. Europol’s March 20 disruption also reinforces the scale and resilience of criminal infrastructure, with more than 373,000 dark web sites shut down and 105 servers seized.
|
Threat level |
Top Risk Theme |
Immediate Focus |
Threat Signal Dashboard
|
|
|
Figure 1. KEV additions by day and Figure 2. event chronology. The clustering on March 20 shows why this week should be treated as a rapid remediation window, not a normal patch cycle.
Key Developments
|
Date |
Development |
What it means for a bank |
Priority |
|
Mar 18 |
SharePoint added to KEV |
Validate any on-prem SharePoint estate immediately. Collaboration platforms remain attractive pivot points into identity, files, and privileged workflows. |
Immediate |
|
Mar 19 |
Cisco firewall management flaw added to KEV |
Treat firewall management as crown-jewel infrastructure. A compromise here can weaken segmentation, policy enforcement, and trust in controls. |
Immediate |
|
Mar 20 |
Five new KEV additions across Apple, Craft CMS, and Laravel Livewire |
Broaden patch focus beyond Microsoft and perimeter systems to mobile platforms, marketing sites, customer-facing portals, and internal web frameworks. |
High |
|
Mar 20 |
CISA/FBI warning on phishing of commercial messaging accounts |
Executive, fraud, treasury, and incident-response staff should be treated as high-risk targets for trusted-channel phishing and account-link abuse. |
High |
|
Mar 20 |
Europol disruption of large dark web platform network |
The criminal enablement layer remains industrialized. Disruption helps, but phishing and fraud infrastructure can re-form quickly. |
Monitor |
Decision Visuals
|
|
|
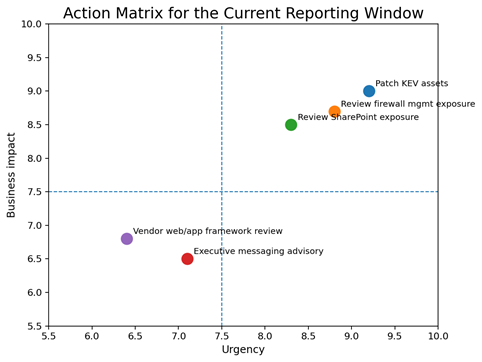
Figure 3. Action matrix for the current reporting window. Figure 4. Scale indicators from Europol’s March 20 operation. For leadership, the main message is that the urgency sits with exposed management platforms and trusted communications, while the criminal ecosystem remains large enough to sustain continued phishing and fraud pressure.
|
Next 72 hours
|
|
Next 30 days
|
Leadership Takeaway
From March 18 through March 25, the most important lesson is that attackers continue to gain leverage by targeting the systems that manage trust: SharePoint for collaboration, firewall platforms for control, messaging accounts for communications, and common frameworks for application delivery. For a bank, the best defensive return this week remains practical and disciplined: patch KEV items quickly, treat management platforms as crown-jewel infrastructure, and tighten defenses around executive and privileged communications channels.
Source Notes
- CISA, “CISA Adds One Known Exploited Vulnerability to Catalog,” published March 18, 2026 (CVE-2026-20963, Microsoft SharePoint).
- CISA, “CISA Adds One Known Exploited Vulnerability to Catalog,” published March 19, 2026 (CVE-2026-20131, Cisco Secure Firewall Management Center / Security Cloud Control).
- Cisco Security Advisory, “Cisco Secure Firewall Management Center Software Remote Code Execution Vulnerability,” March 2026 bundled publication.
- CISA, “CISA Adds Five Known Exploited Vulnerabilities to Catalog,” published March 20, 2026 (Apple, Craft CMS, Laravel Livewire).
- CISA and FBI, “Russian Intelligence Services Target Commercial Messaging Application Accounts,” published March 20, 2026.
- Europol, “Global cybercrime crackdown: over 373,000 dark web sites shut down,” published March 20, 2026.
- NVD entry for CVE-2026-20963, updated March 18, 2026, describing a SharePoint deserialization flaw that allows authorized attackers to execute code over a network.